Remote working: a phenomenon that has gained more and more popularity around the world. There are good reasons why this is the case, since studies show that it can save up a lot of time and costs.
a study from the first three months of the COVID-19 pandemic showed that U.S. citizens saved about 65 million hours of commuting. Daily, that is. Not only does working from home save a lot of time, it also boosts the performance of employees. If people can work from any place they want, their performance increases by about 22% if we believe the study conducted by the world leading Stanford University. There seem to be sufficient reasons to let people work from home, both in terms of effectiveness and efficiency.Remote working is only possible because of one thing: online work. But, online working obviously isn’t limited to the remote environment. Most of the jobs today require some form of connection to the internet in order to be done adequately.
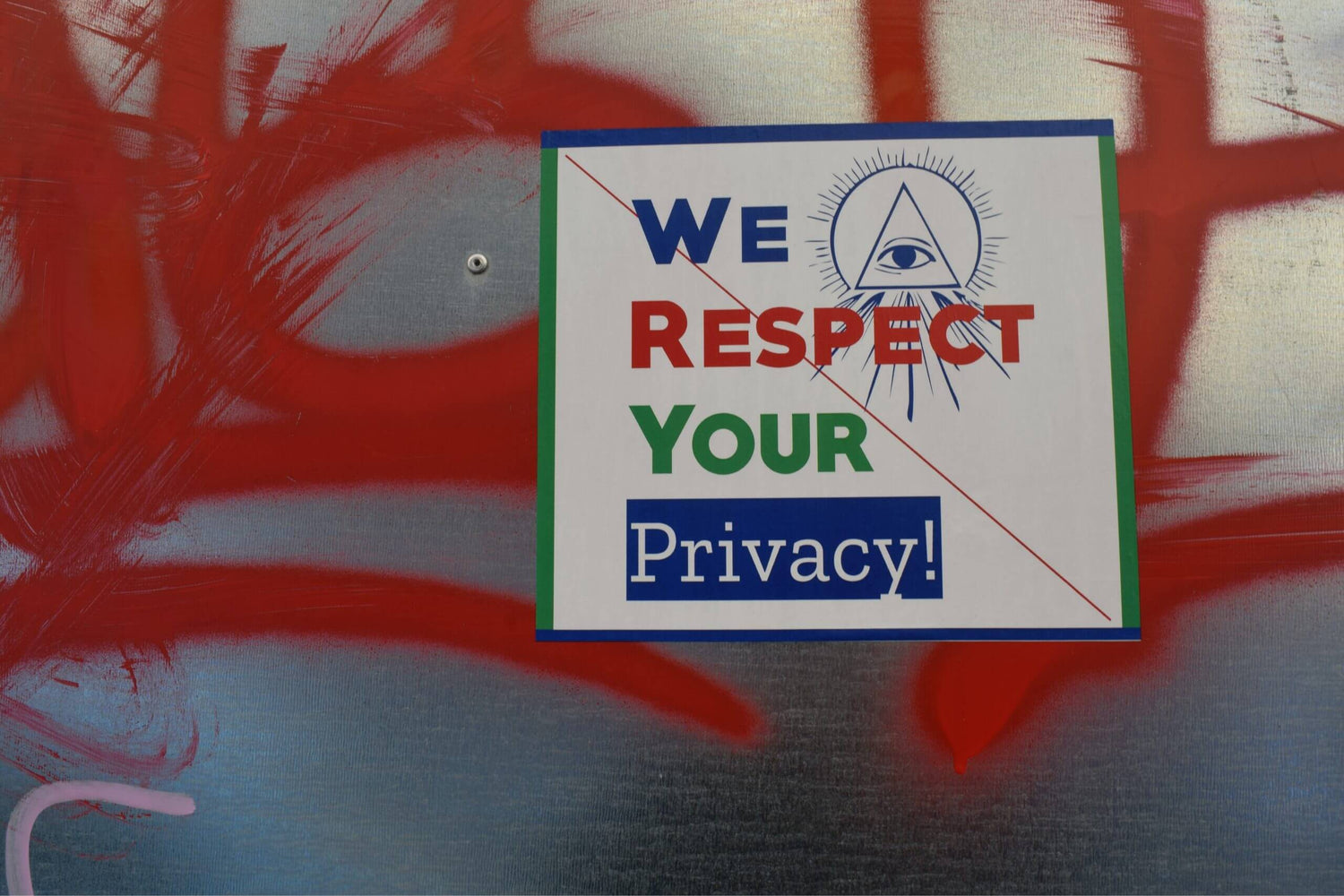
Ideally, the employer can guarantee privacy when working online. Besides, it can ideally guarantee the same privacy at the office as well as when working remotely. But, actually, this can never be the case. A lot of factors come into play when it comes to privacy. Therefore, the expectation of privacy while working remotely can hardly ever be fulfilled.
What is meant with expectation of privacy?
Two types of expectations can be distinguished when it comes to the expectation of privacy. First of all, the subjective one. This varies greatly between individuals and is mostly an opinion. The second one is the objective, or legitimate, expectation of privacy. This is rooted in legislation or policy of the company.
The objective expectation of privacy can, for example, be that companies provide a safe space where no data can be leaked. In the U.S. there is also the fourth amendment, which makes such expectation of privacy legally binding.
Expectation of privacy and remote working
However, the boundary between objective and subjective becomes a bit murky when applied to working remotely. For example, places where individuals expect privacy include residences and hotel rooms. Other public spaces like libraries and working cafes are expected to have a certain level of privacy. But, how can an employer provide this privacy?
Privacy online
So that means, although we work more and more online, our privacy becomes evermore uncertain. This has a lot to do with the use of different spaces. But, it also has to do with the very idea that you’re working online.
Let’s go back to the fourth amendment. It turns out, although it is legally binding, cybercommunication does not fall under the legislation. It is evident that only through strong political desire, such problems will be solved. Unfortunately for (remote) workers and employers, this political desire isn’t very high at all.
Privacy problems that can arise while working online
The tracking of data is a valuable source for hackers and institutions. There is a widespread consensus that data privacy is becoming more and more important in a world that is evermore reliant on data collecting machines. Since the law is lacking to secure this privacy, companies have to take matters in their own hands.
So, the problem in general when working online is the hacking of data that is generated by you or your company. This, too, includes the data of your affiliates or clients. For example, T-Mobile had a huge data breach that laid bare the personal information of millions of people. This also included credit card information.
Besides, cameras of phones, laptops, and computers are easily hacked. Through hacking the camera of such devices, anyone can see what you are doing. For example, if anyone within or outside your company has bad intentions they can quite easily hack your camera and spy on you.
Privacy problems that can arise when working remote
The main privacy problem that can arise when working remotely is a hacking technique known as juice jacking. It basically means that public charging points are physically modified by hackers. The exact points with which the USB cable connects with the USB charging point are modified, and the connection that is made between the smart device and the USB is exploited. This way, malware can be installed onto devices without any notification or consent. Any device that can be charged via the USB ports is prone to juice jacking, from iOS to Android to BlackBerry and anything in between.

How to comply with the expectations of privacy as an employer or employee?
As indicated, the expectation of privacy can’t be met in an online environment. Or, at least the one that is legally binding. Of course, some people might not care about someone hacking their camera or collecting all their personal information. But, for the ones that do, there are several ways to protect your privacy. Actually, for remote workers it might even be easier, since some countries require compensation for remote working. It wouldn’t be a mistake to use this budget to increase your privacy online.
USB data blocker or JuiceBack charging cable
Although it can have severe consequences, the problem of juice jacking can easily be overcome. When charging at public charging stations, using a USB data blocker would be an easy solution. If you’re not a fan of the small size of the USB data blocker, you could also opt for the JuiceBack cable: a charging cable with built-in USB data blocker for USB-C or Apple products.
Camera slide and iPhone privacy case
To make sure that nobody can enter the camera of your laptop or computer, the webcam cover provides the best solution. In case you own an iPhone, the problem is pretty easily solvable by using an iPhone privacy case.
By taking matters in your own hands, you will always be safe from any place you are working.